WordPress Tutorial
WordPress 6.3.2 Security Update: A Crucial Fix for 8 Vulnerabilities
Table of Contents
Introduction
If you use WordPress for your website, maintaining top-level security should be top of mind. Failure to do so exposes both content and user data to cyber threats, while updates like WordPress 6.3.2 aim at patching existing vulnerabilities. Here we discuss every aspect of this new release as well as eight security loopholes it addresses as well as ways to update WordPress safely and efficiently.
Ultimate Guide to Create Ecommerce Website
Whether you are interested in starting a new online business or you want to expend your existing business online. Click the button below read full step-by-step ultimate guide
Key Features of WordPress 6.3.2 Security Update
Focused Security Patches
This update specifically targets 8 security flaws–ranging from minor nuisances to potentially devastating vulnerabilities–that threaten the health and viability of websites. Each patch in this update neutralises one such threat, making this upgrade essential in protecting the site.
Timely Release
At a time when cyber threats become ever more sophisticated, timely updates such as these are absolutely essential to ensure the protection of online assets. WordPress takes pride in promptly providing these updates so as to maintain its users with adequate safeguards against online risks.
User-friendly Implementation
WordPress has made updating a breeze for nontechnical individuals as well.
Details on the Eight Security Vulnerabilities
Cross-Site Scripting (XSS)
WordPress 6.3.2 addresses several major flaws related to Cross-Site Scripting, a potential vulnerability where malicious actors could insert harmful code onto websites and exploited by them for exploitative gain.
SQL Injection
SQL injections have become an increasingly common tactic used by hackers to gain entry to databases. With this update, your website is protected against such illicit activities and any possible intrusion attempts.
Broken Authentication
Another vulnerability that made it into the list was broken authentication. This one gives unauthorized users potential access to privileged accounts.
Security Misconfiguration
This update also addresses security misconfiguration, an often neglected task that exposes sensitive data to unwanted individuals.
Exposed Sensitive Data
Protecting sensitive data like passwords and personal information forms the bedrock of website security. WordPress 6.3.2 takes care of this flaw effectively.
Cross-Site Request Forgery (CSRF)
This vulnerability could allow attackers to lure authenticated users into taking unwanted actions. WordPress 6.3.2 addresses this bug.
XML External Entity (XXE) Attacks
This update also addresses XML External Entity attacks and prevents external entities from accessing and corrupting your website.
Unvalidated Redirects and Forwards
Although not as severe, this flaw nonetheless poses a potential security risk by redirecting users to potentially fraudulent websites and setups.
How to Update to WordPress 6.3.2
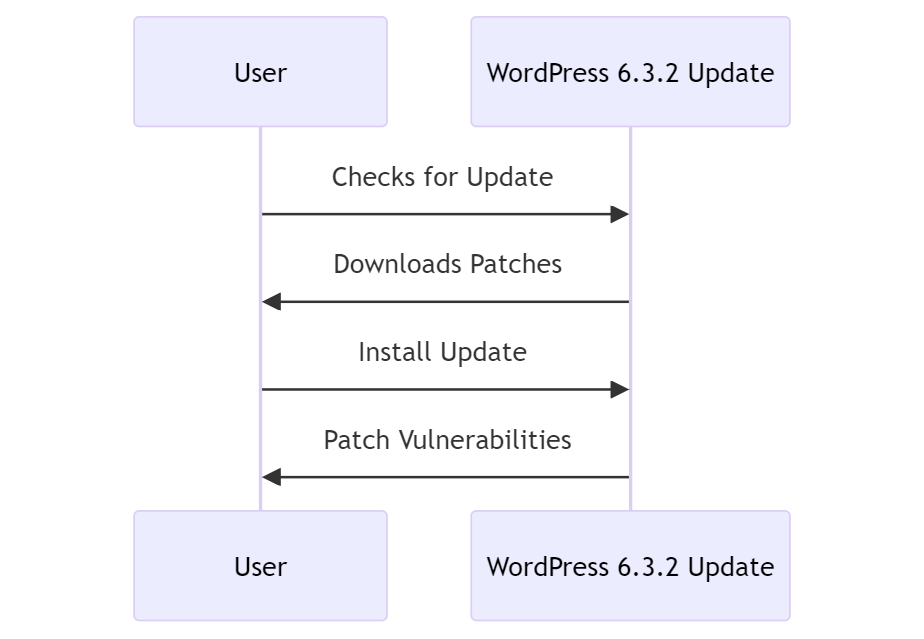
For a successful update, adhere to these steps:
- Backup Your Data: Safeguarding your existing content is paramount.
- Check for Compatibility: Validate that your existing plugins and themes are compatible.
- Initiate the Update: You can do this via the WordPress dashboard or manually.
- Verify the Installation: Once updated, run a full site check to ensure that everything is functioning smoothly.
Read the official WordPress security release announcement:
WordPress 6.3.2 – Maintenance and Security release
Conclusion
If you value the safety and integrity of your website, installing WordPress 6.3.2 Security Update should be on your immediate to-do list. In addition to patching eight vulnerabilities, this update also enhances website security infrastructure – so update now and stay safe against cyber threats!

